The role of artificial intelligence in authentication
Find out why AI is so important and what opportunities it will offer in the future.
Identity verification and authentication are required by law in many industries. These regulations play a crucial role in the fight against economic and financial crimes such as fraud, identity theft and money laundering, as well as for private and economic security. Originally, authentication and verification procedures were carried out manually, a time-consuming process that required painstaking attention to detail and a lot of manpower.
As technology has advanced, new digital methods have been developed to systematise authentication and verification procedures and make them more reliable than the traditional, manual processes. The use of artificial intelligence (AI) in these processes has vastly improved their precision, efficiency and ease of use. In the following, we will take a closer look at AI and its role in authentication.
AI & AUTHENTICATION PROCESSES Introduction to artificial intelligence
Artificial intelligence, also known as AI, is a broad term for various types of experience-based data processing techniques designed to mimic human development, thought leadership and decision making. Through analysis, experience and data collection, AI can learn new skills, detect fraud and overcome language barriers, among other things. Artificial intelligence has not only proven itself in numerous industries, but has even become the standard for data authentication, identity verification, object recognition in medical imaging, personal assistance technology and many other processes.
The skills of AI can essentially be divided into four disciplines: machine learning, natural language processing (NLP), automation and robotics, and machine vision.
Machine learning: Machine learning is the foundation of AI. This technique is used to develop and refine skills based on experience. Deep learning is a more advanced form of machine learning that uses multiple layers of neural networks to process, analyse and learn from data. On this basis, human-like decisions can then be made, new skills acquired and work performed independently of human supervision.
Natural language processing: Natural language processing (NLP) is an AI technique for processing written and spoken language. This includes translating languages into written and audio formats, editing texts, composing written content and generating audio responses. NLP is used, for example, in interactive voice response (IVR), translation programs, grammar aids and word processing programs.
Automation and robotics: Automation and robotics are two independent forms of artificial intelligence that are often combined in practice. As the name suggests, automation ensures greater efficiency and accuracy by automating frequently recurring, monotonous and time-consuming tasks. It is used, for example, for fraud detection in financial institutions or for data entry and management in day-to-day business. While automation was designed for computer-controlled tasks, robotics is relevant for performing physical tasks, such as assembly line work in production or certain high-precision surgical procedures.
Machine vision: Machine vision, also known as computer vision, is an AI technique that converts images into data that can then be automatically analysed and examined for inconsistencies. Machine vision is the basis for commonly used functions such as document authentication, identity verification, or object and face recognition. This process is useful in many areas, but has become an indispensable tool in the healthcare and financial sectors in particular.
AI & MACHINE LEARNING Development and significance of machine learning for AI
The term artificial intelligence first appeared in the 1920s and was popularised by science fiction. By the 1950s, however, the idea of artificial intelligence had already developed from a mere concept into an official subject of research. At that time, computers already existed, but their functionality was limited to the simple execution of commands. As computers had neither a hard disk nor the corresponding memory capacity, the entire process was immediately lost again once a command had been executed. This is where machine learning initially came in.
Since its inception, machine learning technology has been developed and refined in leaps and bounds. It started with simple chess programs and the first robots; since then, machine learning has grown considerably and has become the basis for most AI processes and algorithms. Algorithms are coded solutions for individual technical problems. Depending on the objective, there are simple to highly complex algorithms that can process or calculate many types of data to generate the desired result. As machine learning is the foundation of AI and technology as a whole, it is used virtually whenever technology is used.
AI & AUTHENTICATION Artificial intelligence in authentication
While verification involves first checking a person's identity against their ID documents, subsequent authentication involves checking whether the person attempting to access an account or sensitive information is actually the person in question. There are three types of authentication:
- Something you know: password, PIN, personally identifiable information (PII) or the answer to a security question.
- Something you have: Objects, such as key cards or identification documents.
- Something you are: facial or iris recognition, fingerprints or other biometric data.
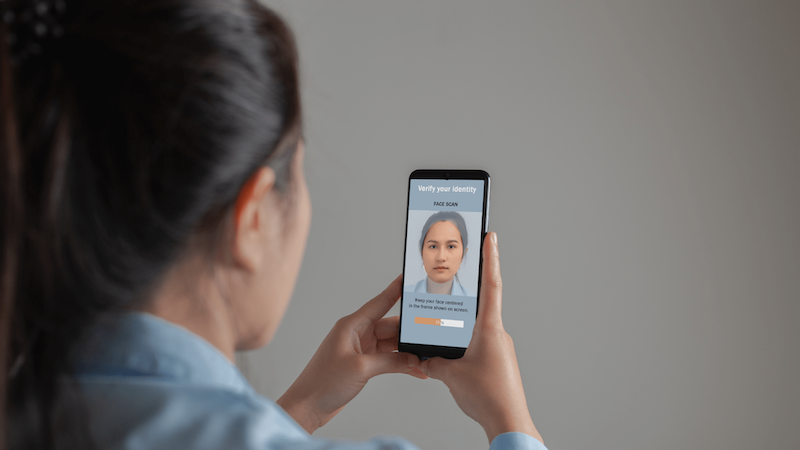
The first type of authentication is traditionally the most widespread. However, due to the high number of hacker attacks and data breaches, multi-factor authentication - an example of the second type of authentication - is now preferred to ensure data security. Of the three types of authentication, the third is the most secure. This authenticator could also use AI technology to recognise whether the person is actually present, also known as "liveness detection".
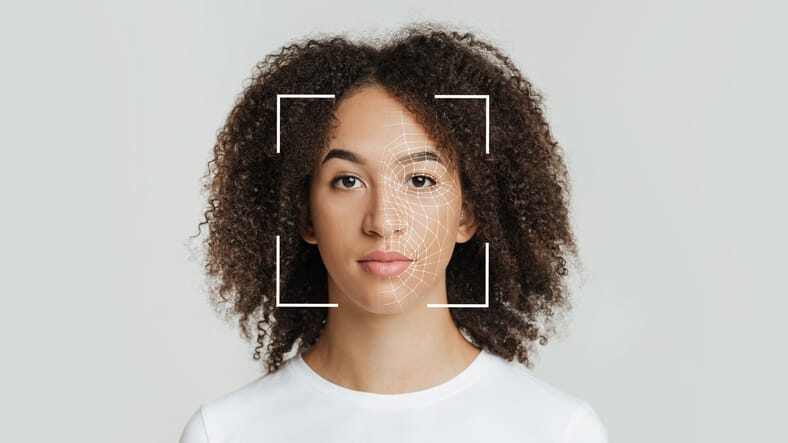
During the verification process, biometric data can be collected as a further means of authentication. There are two types of biometric authentication: simple biometric authentication and behavioral biometric authentication. An example of biometric authentication would be capturing a thumbprint or facial recognition to access an account. Behavioural biometric authentication captures behavioural patterns such as moving the mouse, scrolling and clicking with a touchpad or typing on a keyboard. These behavioural indicators are carefully analysed to determine whether the movements were performed by a human or a computer.
With AI as part of the authentication process, security has been significantly improved and the number of malicious cyberattacks and data breaches reduced. AI has also enabled companies to expand their offering and customer base, process data efficiently, while providing a seamless and user-friendly authentication experience.
AI & CHALLENGES Challenges and reservations
AI in authentication is faster, more reliable and more efficient than manual authentication processes that rely on human attention to detail and accuracy. However, the widespread use of AI in authentication and similar processes involving personal data or public safety also raises concerns about privacy compliance, the ethics of using AI in the military, and the safety of emerging technologies such as self-driving vehicles.
Although AI in authentication has a positive track record in fraud detection and data security, the reliability, accuracy and potential risks involved are still being put to the test. As with any innovation, there is still plenty of room for improvement. AI algorithms are constantly scrutinised by their developers and the public. While updating and developing new algorithms is a large area of work, it usually leads to greater data security, fraud prevention and user-friendliness. Despite the inevitable challenges and concerns that arise with AI in authentication, the predictions for the future remain promising.
AI IN PRACTICE Practical areas of application
AI-driven authentication in the financial sector
Financial institutions are responsible for the protection of their customers' personal data and financial assets, fraud prevention and economic stability. This responsibility comes with great risks and serious consequences should security breaches, fraudulent activities or other forms of financial crime occur. To prevent illegal activities, financial institutions must adhere to certain KYC (Know Your Customer) regulations. Authentication and verification procedures must be constantly evolving to reliably detect suspicious activity and prevent crime.
Thanks to significant technological advances, financial institutions can now offer user-friendly digital services via online portals and smartphone apps. As traditional authentication methods relied on unreliable human skills and attention to detail, AI has become the standard in authentication. AI-powered authentication tools such as PXL Vision's PXL Ident use state-of-the-art AI algorithms and biometrics to ensure regulatory compliance, consistent fraud detection and ease of use.
Security of healthcare and patient data
The introduction of AI in healthcare has triggered a wide range of reactions. Its direct use in medical practice and research has raised concerns about the security of patient data, while its use in authentication has made online healthcare portals and telemedicine safer and more user-friendly.
To access digital health portals, patients must use AI-driven multi-factor authentication. This method ensures a good balance between increased security, ease of use and convenience. In addition, AI-driven authentication can be used to protect patient data in hospital databases and prevent data breaches. Due to the sensitivity of patient data, a security breach could be detrimental to both the patient and the institution. AI in authentication is an important part of healthcare as it provides the highest form of security that currently exists.
Conclusion
The use of AI in authentication enables companies to stay one step ahead of cybercriminals and fraudsters. Given the current state of affairs, the future outlook for AI in authentication is positive and full of opportunities for growth and progress.
As AI technology continues to evolve and adapt to new regulations and international rules, it will either maintain its pre-eminent position in the field of computing or be overtaken by a similar, more powerful new invention, quantum computing. Regardless of future developments, the use of AI in authentication has significantly improved data security and user-friendliness, making it irreplaceable today.
FAQ
AI verification is a process that checks and confirms that the AI technology complies with all applicable regulations.
There are three types of authentication: (1) something you know, (2) something you have, and (3) something you are. The first type requires information such as a PIN, a password or the answer to a security question. The second type is a tangible thing, such as an ID or access card. The third type of authentication uses an individual characteristic, such as a fingerprint, voice recognition or a facial scan.
AI biometrics refers to the integration of AI with biometric systems. In combination, they are used to identify and verify people based on their physical characteristics or behaviour. This technology includes functions such as facial recognition, fingerprint recognition and voice recognition.
A key function of AI in biometrics is life detection. Here, AI algorithms verify the presence of a person in real time and ensure that the person is physically present during the verification process. This helps to prevent fraudulent activities, such as the use of photos, videos or masks to impersonate another person.
.png?width=126&height=101&name=logo%20(2).png)
.png?width=63&height=51&name=logo%20(6).png)




