Information security, or infosec as it is commonly called, is the practice of protecting information by preventing or at least reducing the probability of unauthorised access to data. Information security has a long history – spanning from early recorded instances of Julius Caesar’s Caesar cipher (circa 50 B.C.), to the 1st and 2nd World Wars that tore Europe apart — hastening the invention of the Enigma machine.
Nowadays, emails/usernames and passwords are the primary methods used to access and protect our personal information. This is, of course, logical as the flow of our sensitive information has largely moved onto digital channels, evermore so as our world becomes more internet-connected.
This move towards digitalisation and internet connectivity is in fact so relevant that another term, “cybersecurity”, which has to do with the security of computers and computer networks, is often used interchangeably with information security.
CIA: the three principles of information security
There are three primary principles of information security expressed by the acronym CIA. Not for the Central Intelligence Agency (CIA) in the US, but rather for the terms: confidentiality, integrity, and availability. However, it is likely that the CIA in the US also applies the CIA rule when it comes to their own information security.
Confidentiality – data is confidential only when those people who are authorised to access it can do so. In order to ensure confidentiality, you need to be able to identify who is trying to access the data and to block attempts by those without authorisation. Unique usernames and strong passwords along with two-factor authentication (covered below) provide varying levels of defence against penetration attacks.
Integrity – implies maintaining the data in its owner-defined state as well as the prevention of attacks or accidental mishaps that could lead to unsanctioned modification. Many of the techniques that ensure confidentiality will also protect data integrity. Data that is protected by strong passwords and other similar infosec techniques is more likely to retain its integrity.
Availability – functions in the opposite sense to confidentiality. While it is important to protect your data from unauthorised access, you also need to ensure that it can be accessed by those who have the proper permissions. Information should be made available to those who have the username and password.
Most users of the internet are only concerned with the confidentiality and availability aspects of infosec, given that the integrity of their data is generally the concern of whichever online services they might be using. The username or email and password combo is where the responsibility of the individual computer user lies today. However, infosec at this point can be a rather contentious topic, especially for individuals who are relative newcomers to the internet and computer technology. Most notably here are those who were already much older or from a country currently in the early stages of internet and widespread computer adoption.
Information security in the digital age
By now, most of the developed world is connected to the internet. And while this connectivity, alongside the internet’s growing user base and high number of services that are moving part or all of their services online brings massive benefits to all involved, severe infosec issues are also on the rise. In particular, the pervasiveness of hackers on the world wide web, who take advantage of unsuspecting users is increasing.
To wit, most services that individuals engage with on the internet requires setting up an account, which normally requires entering in an email/username and password. That is fine in and of itself except that many people reuse the same password and username combination for multiple accounts. This activity can and does turn out disastrous for the individual who has their single username/password cracked. Hackers who manage to crack a password will try the same password or slight variations of it on other accounts of the same user.
It is safe to say that most people have experienced a software attack of one form or another, whether through a virus, Trojan horse or by being lured into a phishing attack. It is also possible that your information has been compromised but that no attack has yet been tried. To help prevent and counteract these attacks, we are instructed about password ethic and warned not to click on any links or enter any personal information on pages that we are not 100% certain about.
Passwords: Single-factor authentication
However, this overt carefulness also adds friction to our online activities and at the end of the day, no matter how careful we are, we are also at the mercy of the online services and companies that we interact with and store our personal information with. Data breaches are all too frequent, and our emails and other sensitive information are regularly leaked. Check your email at Have i been pwned?, to see if you have fallen victim to an online hack. The chances are good that you have.

Passwords that are short and simple enough to remember tend to be very easy to crack. A password checker can be used to verify this. On the other hand, passwords that are long and complex enough to be uncrackable are essentially impossible to remember.
All of this is not to suggest that we do away with usernames and passwords as they certainly serve their purpose, especially with regards to the availability aspect of the CIA acronym. There are some partial fixes such as password managers, and while these programs come highly recommended they still require a certain level of trust of the software that you end up deciding to use. Rather, online information security requires something more. One solution is to use two-factor or multi-factor authentication techniques.
What is two-factor authentication (2FA)?
Two-factor authentication (2FA) or multi-factor authentication, as it is also called, is the act of using more than one factor or method to prove one’s identity. This differs from single-factor authentication which, in online cases, is the username and password combo.
When you visit a bank to withdraw some money (who does that anymore?) the bank teller asks to see your bank card and a piece of photo ID. The bank teller checks the bank card and ID to make sure they are still valid, have your name on them and that the ID contains your photograph. If the photo and name match the person, then the teller can verify that you are who you claim to be. The next step of the process would involve using your bank card by inputting your secret pin number. These two steps combined is an example of two-factor authentication.
However, in the online space, the process of authentication is a little bit different because you are no longer relying on a person to verify and authenticate that you are who you say you are, but you are instead entering your mostly private username and totally private password into an online account. If someone other than you illegitimately gains control of your username/password, they can then pretend to be you by simply entering in the information online. This is precisely why online multi-factor authentication has become really important in recent times.
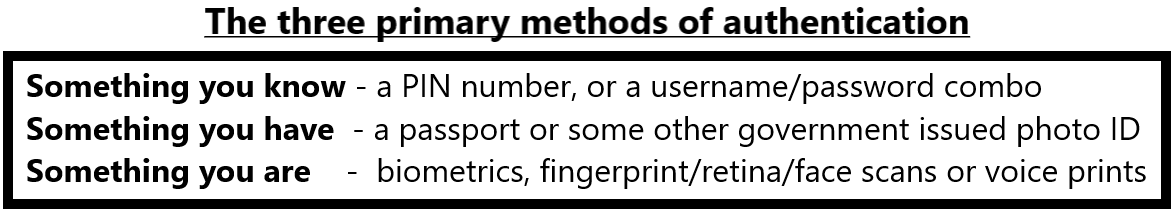
The act of providing proof in order to authenticate oneself is generally divided into three different categories. These are: something you know, something you have and something that you are.
How can facial authentication technology help with information security?
Facial authentication technology uses face scans in order to add an extra level of protection to your login process. In the above box on primary methods of authentication, face scans are categorised as something you are and it is clear that your face belongs to you. Facial authentication technology offers a superior level of account protection especially when combined with strong usernames and passwords.
After the user has been verified using their username and password, the user’s face can then be used for further account authentication. A face scan can be used as a second factor and incorporates sophisticated algorithms that can pick out the slightest abnormalities and either grant or reject access to the user.
Passwords and facial authentication technology
Long and complex passwords coupled with the use of a variety of different usernames/emails is one of the easiest and best ways to stay safe online. However, doing so would require a password manager (unless you are gifted with a didactic memory) which brings forth a host of other potential issues. What happens if you forget your master password? Or somebody cracks your master password? or you inadvertently leave your password manager logged-in on a device allowing access to all of your passwords?
In these cases, two-factor authentication could be your saviour and it should be employed whenever possible. One of the best ways to accomplish 2FA right now is through facial authentication technology. Fingerprints and retina scans, while still okay for most purpose, have all been proven as beatable, most publicly by the German-based Chaos Computer Club.
All of the major smartphone companies have integrated facial recognition technology into their newest devices. The top 4: Samsung, Huawei, Apple and Xiaomi have different names for the tech but the algorithms used are similar. Furthermore, because traditional authentication methods are no longer sophisticated enough to keep up with today’s advanced fraud landscape, high-risk industries like banking and finance are turning to face-based identity authentication and verification instead.
PXL Vision is a leading provider of facial biometric technologies
Get in touch with us today to learn more about our innovations in facial biometrics and how our flexible and modular product solutions can assist your business today.
.png?width=126&height=101&name=logo%20(2).png)
.png?width=63&height=51&name=logo%20(6).png)








.jpg)



