Two-factor authentication, or 2FA in short, serves as an indispensable protective shield in our digitally connected world. It effectively protects personal data against the ever-growing threat of cyberattacks and data leaks.
Since 2019, two-factor authentication (2FA) has been statutory for online banking services within the European Union. This security measure is also reflected in usage habits. In Germany, approximately 49% of users make use of 2FA not only for banking, but also for at least one other online service. On the contrary, only about 28% of users in Switzerland regularly use 2FA to protect their personal login details.
Two-factor authentication is proving to be one of the most robust measures for safeguarding privacy. At PXL Vision, we also apply this security method: Our customers often integrate 2FA into the customer journey and combine it with our identity verification solutions. It is also possible to use the validation of email address or mobile number directly in the PXL Ident workflow as a separate module before the actual identity verification with PXL Ident starts. In this way, we always set up a secure communication channel with two-factor authentication first. But why is that useful?
Definition of Two-Factor Authentication
Two-factor authentication also enhances the security procedures of conventional login methods with usernames and passwords. It protects access to online accounts and services, by also requiring a second form of authorisation.
Due to the combination of two or more factors, 2-step authentication provides greater security compared to systems that rely on mere passwords. At a time when cyberattacks are becoming increasingly sophisticated, this additional security barrier is especially important. To obtain access to an account, a potential attacker must not only crack the password, but also overcome the second factor. Therefore, 2FA is a crucial line of defense in maintaining digital security and privacy.
Methods: What is Two-Factor Authentication?
In addition to a password, two-factor authentication requires a second factor. This second layer of security can be diverse: from mobile authentication apps to one-time codes or special hardware tokens, all the way to biometric authentication using fingerprint scans and facial recognition.
Authentication Apps
A widely used method of two-factor authentication is the utilization of authentication apps. Some examples of this are Google or Microsoft's two-factor authentication apps: Google Authenticator and Microsoft Authenticator respectively. Authenticator apps generate timed single-use passwords (TOTP) that change every 30 seconds. After the user synchronizes the app with their account, they will receive the one-time code that must then be entered when logging in.
One-Time Code using SMS or E-Mail
Another common method consists of receiving a one-time code per SMS. After entering the password, the system will send a code to the user's registered phone number or e-mail address. The code will be entered when logging in. This method is the simplest to use and therefore also the most popular method for users, since they don't need any additional tools or apps. This can be seen, for example, in Apple two-factor authentication.
Hardware-Token
Another example of two-factor authentication is hardware tokens. These devices can either be USB tokens or NFC-enabled (Near Field Communication) devices that also generate one-time passwords. To provide a second factor, the user will keep the token with them and use it during the login process. Hardware tokens deliver an additional layer of security; however, an appropriate device is required.
Two-Factor Authentication with Biometric Identifiers
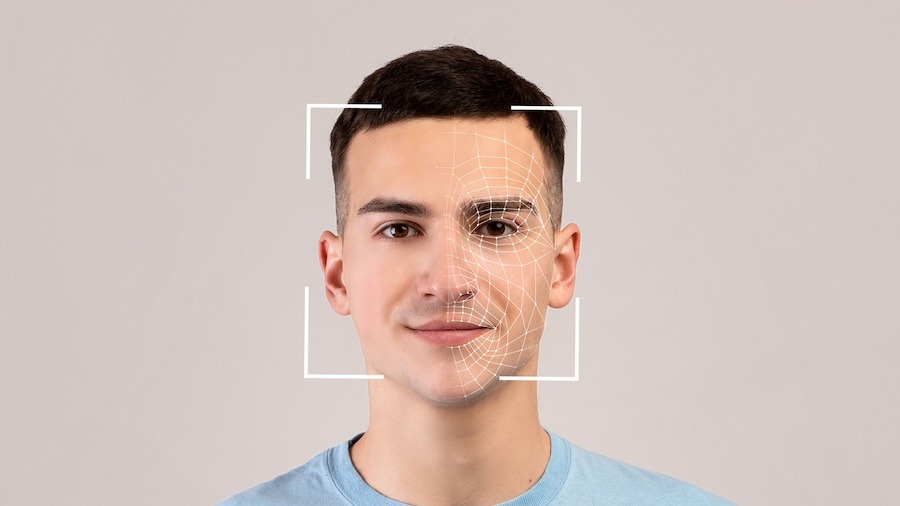
An advanced method of two-factor authentication is an identity check with biometrics. Biometric authentication uses unique physical identifiers such as fingerprints, facial features, iris scans, voice recognition, or palm vein scans.
During the initial registration, biometric data will be stored in encrypted form. During subsequent authentication attempts, the recorded identifiers will be compared to the stored reference. A match will confirm the identity and enables access. Biometric data provides high accuracy and reliability due to its uniqueness and protection against forgery.
What Should Be Considered When Choosing a 2FA Method?
Not all two-factor authentication methods provide the same level of security. For example, authentication through an SMS code is considered less secure, as SMS can be intercepted or susceptible to phishing attacks.
On the contrary, two-factor authentication with biometrics provides a high degree of security through the use of individual physical identifiers. The distinctiveness of these identifiers makes them extremely difficult to falsify and significantly complicates potential attacks.
At the same time, biometric authentication enables a pleasant and straightforward user experience. Compared to traditional passwords or codes, the identification process becomes faster and more natural with the help of biometric features. Scanning a fingerprint or using facial recognition is easy and requires little effort.
However, data protection plays a central role in the use of biometric identifiers, as this data is highly sensitive and unique to each person. Therefore, it is crucial to store and process such information securely and protect it from unauthorized access in order to safeguard user privacy.
How do I Set Up Two-Factor Authentication?
Two-factor authentication combines two different identification factors to secure access to an account or service. This works in just a few simple steps:
- Enter the first factor (Password/PIN): To begin, the user will enter their password or PIN and will then be prompted to provide the second factor.
- Generating the second factor: The second factor will be generated. This can, for example, be a one-time code sent through SMS to the user's phone or take place through an authentication app. Alternatively, it can also be a biometric identifier, such as a fingerprint scan or facial recognition.
- Enter the second factor: The user will enter the one-time code they received or carry out the biometric identity check.
- Confirmation and access: Following successful verification of both factors, access to the account or service will be granted.
Where does Two-Factor Authentication Come into Play?
To increase the security of personal data, two-factor authentication is implemented in various fields. It is extensively applied in digital platforms like social media, e-mail services, financial institutions, and companies across a wide range of sectors.
In particular, platforms that manage sensitive information or store personal data, are relying more and more on 2FA. Banking apps, e-commerce websites, Cloud services, and even gaming platforms are increasingly integrating two-step authentication to protect accounts from unauthorized access and thereby guarantee security for their users.
Furthermore, two-factor authentication is also used in physical access control systems, for example, in companies or government institutions. Here, access is not only controlled via keys or access cards, but also through an additional identity check like biometric features or one-time codes. To effectively secure resources and data, 2FA is particularly relevant in fields where strictly controlled access is required, such as research facilities, government offices, or financial institutions.
Conclusion
Two-factor authentication (2FA) has become an indispensable tool for digital security. It provides an additional level of security that goes beyond conventional password protection and reduces the risk of cyber threats.
There are various 2FA methods, such as authentication apps, hardware tokens, one-time codes or biometric verification. Some of these methods combine excellent security standards with a user-friendly application, such as biometric authentication. The appropriate method for a company always depends on the use case.
Two-factor authentication is adapting to the increasing security threats in the digital world. Through the continual improvement of security protocols and the integration of innovative technology, 2FA can effectively protect our digital identities and data.
FAQ about Two-Factor Authentication
Authentication refers to identities, while authentification confirms the authenticity of objects or information, although "authentification" has become synonymous with "authentication":
- Authentication: Authentication refers to the process of verifying the identity of a person or an object. It is about determining whether someone or something really is what it claims to be.
- Authentification: Authentification (generally called "authentication") denotes the process of confirming the authenticity of an object.
Two-step authentication (2FA) dramatically increases the security of online accounts by going beyond the traditional password. Simple passwords make accounts susceptible to hacker attacks, phishing, or password theft. Two-factor authentication prevents these risks by requiring a second form of authentication, such as one-time codes, biometric data, or security tokens.
Even if hackers obtain the password, access remains blocked without this second factor. Especially with biometric features such as fingerprints or facial recognition, 2FA offers considerable protection against data misuse, since biometric data is highly sensitive. This additional protection significantly minimizes the risk of unauthorized access and misuse.
Although two-factor authentication considerably increases security, no method is absolutely secure. Nevertheless, it makes hacking attempts significantly more difficult and greatly reduces the risk of successful account access on Instagram.
In most cases, it is possible to deactivate two-factor authentication, but this should only be considered if alternative safety measures are available. When possible, you should activate 2FA and leave it as it is to ensure account security.
.png?width=126&height=101&name=logo%20(2).png)
.png?width=63&height=51&name=logo%20(6).png)









%20.jpg)

