Digital Identity Verification
Verify your customers quickly
regardless of location - in less than 30 seconds.
BENEFITS Real-time identity verification
Digital identity verification enables companies to check the identity of their customers in real time before they gain access to their services. Automation offers many advantages:
Fast verification
Identity verification in less than 30 seconds reduces waiting times. This minimises the bounce rate of dissatisfied customers and increases your conversion rate.
Cost reduction
Automation saves time, resources and reduces errors by eliminating analogue bureaucracy and superfluous personnel costs.
Customer satisfaction
Online identity verification enables flexible, convenient and location-independent verification around the clock. This helps you retain satisfied customers in the long term.
Protection against fraud
Prevent identity fraud and support the fight against money laundering. We ensure compliance with the GDPR and DSG with our ISO/IEC 27001-certified process. We are also eIDAS and ZertES conform.
User friendliness
Configurable solutions for different use cases can be easily integrated into existing processes. This means you have no downtime in your day-to-day business.
Higher conversions and profits
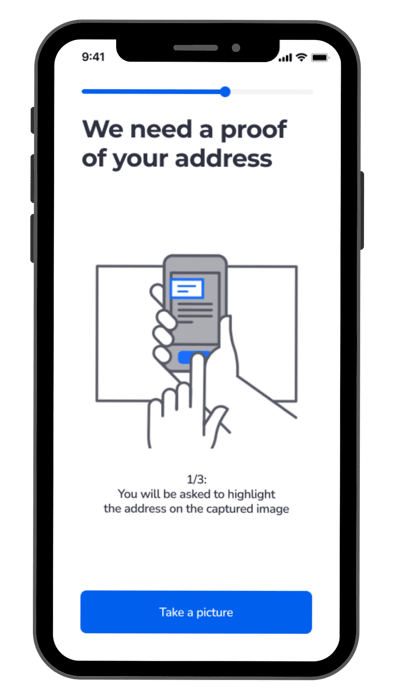
Online identity verification in two steps:
The online identity check works very simply in two steps: it is a combination of document and face verification.
These two verification steps guarantee a reliable identity check and are secure and user-friendly at the same time.
Document verification
- AI-based automatic recognition, classification and capture of proof of identity
- Verification of 40+ security features
- Possibility of biometric NFC chip verification
- Global coverage of documents from over 165 countries
Face verification
- Powerful biometric face verification
- Real-time comparison of the user with the ID document images
- Unique Passive Liveness Detection
No interaction required - Protects against identity theft and impersonation
- Protects against attacks through prints, screens and masks
.png?width=202&height=413&name=animated%20phone%20(1).png)
FLEXIBILITY Digital identity verification for every use case
PXL Vision's digital identity verification solutions are extremely flexible and individually configurable. We provide a modular orchestration that enables platform-independent and customisable integration into existing environments, applications and systems. This means that identity verification can be seamlessly integrated into existing systems without major changes.
To further accelerate the implementation process, we offer you preconfigured workflows that enable rapid commissioning:
- SMS/e-mail verification
- Self-disclosure
- Address validation
- PEP/SL check
- Additional document scan
- Electronic signature
The possible applications of digital identity verification are diverse and range across various industries: from the onboarding process in insurance to a seamless registration process for telecommunication services and secure transactions in e-commerce.
PXL Vision offers a range of integration options and products that can be customised to meet the needs of your business.
GLOBAL COVERGE Global identity verification made easy
Global identity verification is a challenge. The diversity of languages spoken around the world presents a significant hurdle, as identity verification software solutions not only have to recognise numerous languages, but also take their specific characteristics and differences into account.
Added to this is the wide variety of ID documents with different features, formats and security functions. Different legal requirements for data protection and identity verification in different countries also require flexible adaptation of the verification processes.
We offer you secure, global document support in more than 165 countries. Verify customers from anywhere in the world in under 30 seconds and ensure a seamless experience for international customers.
FAQ about digital identity verification
Digital identity verification is a process in which the authenticity of a person's identity is checked online. Digital technologies such as biometric methods, document verification and facial verification are used to ensure that the identity provided actually belongs to the person.
Document verification and biometric face verification are often used for digital identity verification. Document verification checks the proof of identity and facial verification compares the user's face with the image on the document.
Digital identity verification is reputable and reliable. Modern methods such as biometric procedures and document verification offer high security standards to prevent identity theft and fraud.
While local identity verification is based on region-specific data and regulations, global identity verification is more comprehensive. It takes into account a variety of data from different countries and adapts to different legal requirements worldwide to ensure accurate and secure identity verification.
Global identity verification is needed in many situations - especially when conducting international transactions. It is important in industries such as finance and e-commerce, in international real estate transactions and in the verification of users of digital platforms. Finally, it also plays a crucial role in the fight against money laundering and terrorist financing.
READ MORE More on the topic of digital identity verification

Digital Identity Verification explained
What is digital identity verification for business? Learn more about what it is, it’s importance, and different verification methods.
Identity Proofing Explained
Discover what identity proofing is and how it works. Explore the process, examples, and its importance in today’s digital world.

Efficient AML check: digital identification made easy
Digital AML check and identification in accordance with the Anti-Money Laundering Act. Efficient, secure and scalable processes for your company.
Top 10 authentication methods for maximum security
Learn more about the top 10 authentication methods, from MFA to SSO, and how they contribute to identity verification and security.

Authentication vs. authorization: differences & importance
Learn the difference between authentication and authorization and why both are essential for IT security.
.png?width=126&height=101&name=logo%20(2).png)
.png?width=63&height=51&name=logo%20(6).png)




