The top 10 authentication methods for more security
authentication methods, from MFA to SSO,
and how they contribute to identity verification and security.
Authentication methods are now more important than ever. Data has become one of the most valuable resources, so the security of digital identities is at the forefront. Simply entering a password is often no longer enough to protect personal information and business data. Attackers are becoming increasingly clever and resourceful when it comes to bypassing security measures. PXL Vision presents the 10 best authentication methods for better security.
Password-based authentication
Password-based authentication is one of the most basic and commonly used methods of user authentication. This method requires users to enter a username and associated password in order to access a system or application. Although it is simple and widely used, password-based authentication also has its weaknesses. We therefore present some best practices for secure passwords:
- Passwords should be sufficiently long (around 12 characters) and contain a combination of upper and lower case letters, numbers and special characters.
- Use different passwords for different accounts and services. This will prevent a compromised password from enabling access to multiple accounts.
- Change your passwords regularly. This reduces the risk of a stolen password granting permanent access.
- Using a password manager can significantly simplify the management of secure passwords.
Multi-factor authentication (MFA)
Multi-factor authentication (MFA) is an advanced method for securing user accounts and services. Unlike simple password-based authentication, MFA requires the combination of two or more authentication methods to confirm a user's identity.
An example of the use of MFA is the use of SMS codes or mobile authentication apps after entering the password. After the user has entered their password, they receive a unique code on their mobile device, which they must enter to log in. This code changes each time the user logs in and provides an additional layer of security.
The advantages of multi-factor authentication are clear: even if an attacker knows the password, they cannot gain access to the account without the second or third factor. There are various factors for this, including
- SMS codes,
- apps,
- hardware tokens
- or biometric methods such as fingerprint or facial recognition.
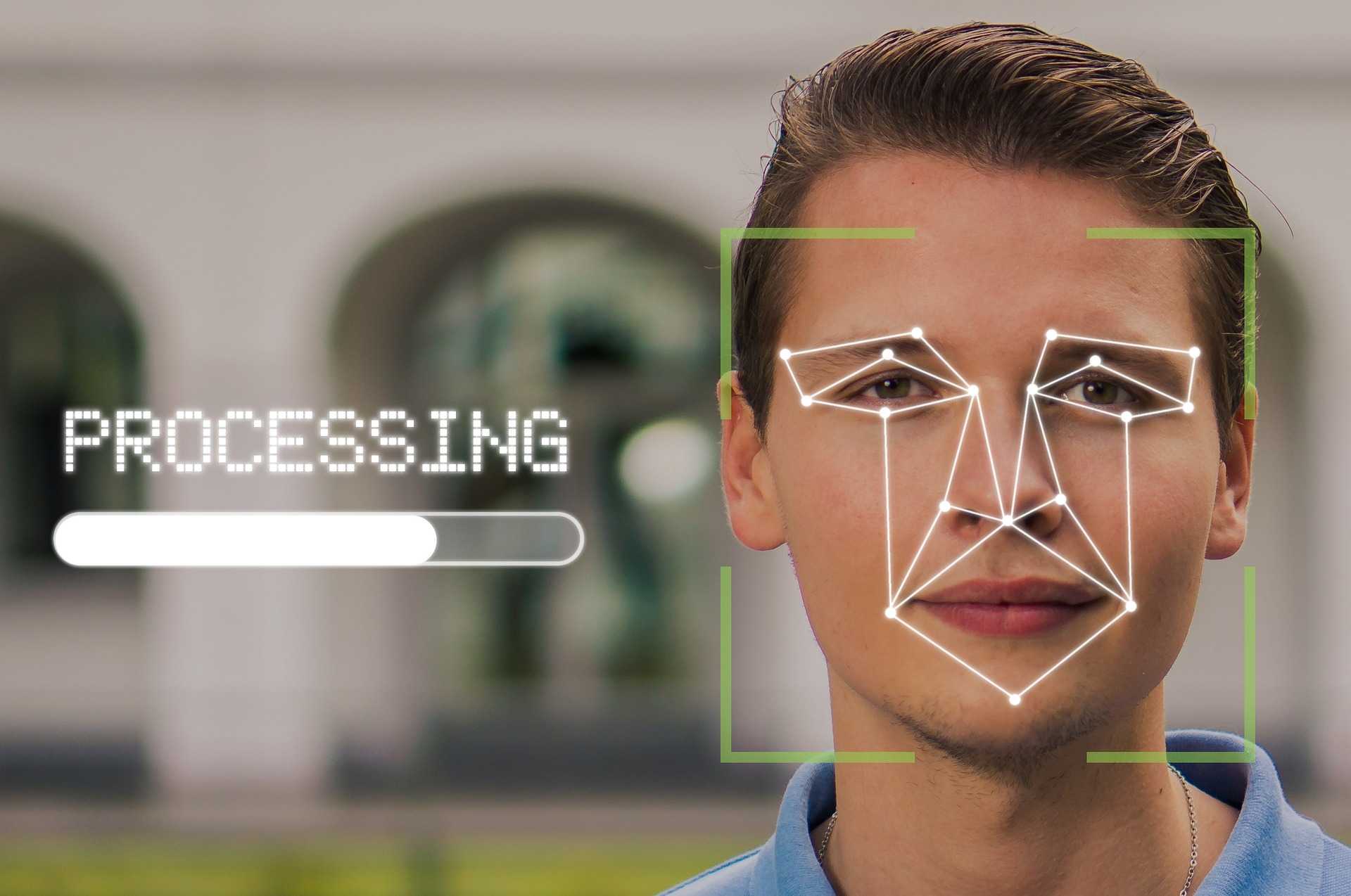
Biometric authentication methods
Biometric authentication methods are a significant development in the field of security technology. They are not based on something you know (like a password) or something you have (like a smartphone), but on a person's individual physical characteristics.
For example, fingerprint scans, facial recognition or voice recognition are used. Fingerprint and facial recognition are widely used in modern smartphones and offer users a convenient way to unlock devices and access protected data. Biometric authentication methods are also used in airports and banks as they offer a high security factor and are very difficult to falsify.
Behavior-based authentication
For behavior-based authentication, movement patterns can be used to identify a user. This can be the gait pattern, for example - because every person's posture and body movements are unique. In practice, behavior-based authentication methods are already being used for building entrance controls.
Electronic signature
Electronic signatures are based on cryptographic encryption methods. The process is based on a secret signature key, also known as a private key, which is used to calculate a unique hash value. This hash value serves as an electronic signature and contributes to non-repudiation. This means that the author of the document, who has been clearly identified by the electronic signature, cannot deny that the document originates from him or her.
With the public key, i.e. the public verification key, anyone can check the integrity of the signature and the affiliation of the corresponding document. The legal framework conditions are strictly regulated and are determined by the eIDAS Regulation.
Video-based authentication
With the video-based authentication method, the user usually has to appear in front of a camera and perform various actions to confirm their identity. These actions can consist of showing an ID card, saying a certain sentence or imitating a predefined movement.
As the method is based on visual data, it is difficult to falsify. It also enables user-friendly authentication as it requires no special hardware and can be used in different environments. However, the quality of the camera and lighting can affect accuracy.
Video-based authentication is used in various industries: this method is primarily used for online services and in the telecommunications sector. It is particularly suitable when the user cannot be physically present to confirm their identity.
Smartcards and physical tokens
Smartcards are handy, portable cards with an integrated chip or magnetic strip. Physical tokens can take the form of USB sticks or key fobs. To ensure security, users must be in possession of smart cards or tokens in order to perform successful authentication.
Even if an attacker knows a user password, they still need physical access to the device to successfully log in. In combination with a password or PIN, the use of a physical device therefore provides an additional layer of security (two-factor authentication). This method is often used in the financial sector, among others.
One-Time Passwords (OTP)
With this authentication method, a temporary password is generated for each login or transaction, which can only be used once. Even if an attacker intercepts the password, it is useless for future access.
SMS-based OTPs are easy to set up and require no additional apps. However, they are more susceptible to security risks such as phishing attacks.
App-based OTP generators offer a higher level of security as they work offline and cannot be easily intercepted. However, as a special app needs to be downloaded, some users find this method cumbersome.
Certificate-based authentication
Certificate-based authentication is a further development of traditional password-based authentication. Whereas with the password-based method, users confirm their identity by entering a secret password, certificate-based authentication uses digital certificates to verify the identity of a user or device. These certificates are issued by trusted certificate authorities (CAs).
Single Sign-On (SSO)
Single sign-on (SSO) is an authentication method that allows users to log in to a system or application once and then automatically access other systems or applications without having to log in again.
A well-known example of SSO is Google services, which can be managed centrally via accounts.google.com. Other platforms also run via a Google account.
SSO significantly improves user-friendliness, as users do not have to log in separately for each application. This saves time and reduces the effort required to remember passwords.

Conclusion
From password-based authentication to biometric procedures and electronic signatures, different authentication methods offer a wide range of options for authenticating identities and protecting access to sensitive information. Often, a combination of several authentication methods is most effective in ensuring a high level of security.
PXL Vision specialises in digital, fully automated identity verification. This method can be used for authentication, but is primarily used for the initial registration of new customers.
For identity verification or identification, we combine a document scan of the ID with a biometric selfie video.
Are you interested in implementing identity verification? Contact us now – we will be happy to advise you.
FAQ
An authentication method is a procedure for verifying the identity of persons or users before they are granted access to specific resources or services.
There are many authentication apps, including Google Authenticator, Authy, Microsoft Authenticator and many more. These apps are often used to generate one-time passwords (OTP) as part of multi-factor authentication (MFA).
The main difference between MFA (multi-factor authentication) and 2FA (two-factor authentication) is the number of proofs of identity required. Multi-factor authentication (MFA) requires at least two different proofs of identity, whereas two-factor authentication (2FA) only requires two proofs of identity, one of which is usually a password. MFA therefore requires an additional layer of security to ensure access to protected systems or data.
.png?width=126&height=101&name=logo%20(2).png)
.png?width=63&height=51&name=logo%20(6).png)




