Know Your Customer (KYC) Advisor
Read all about KYC here.
And find out how our solutions can help you
digitise your KYC processes
DEFINITION KYC Identity Verification
The global increase in Internet usage and the adoption of online services has led to both significant economic growth and criminal activity. Fraud, corruption, money laundering and other forms of white-collar crime are real issues that companies and financial institutions face on a daily basis. To counter such attacks, organisations need to verify the identity of their customers before entering into a business relationship or transaction.
Traditionally, the identity verification process, known as Know Your Customer or KYC, has been a face-to-face meeting. Today, many companies are shifting their KYC processes from the traditional method to electronic Know Your Customer, or eKYC. Replacing KYC with eKYC is a convenient solution for both the company and the customer.
This page outlines the basic principles of KYC and its proper implementation in your business operations.
Understanding KYC
Know Your Customer is a subset of anti-money laundering (AML) regulations. KYC refers to the process of verifying the identity of customers. Know Your Customer and Know Your Client are sometimes used interchangeably. These regulations help protect financial institutions from fraud, corruption, terrorist financing and money laundering. KYC is a mandatory process, so financial institutions that fail to comply can face fines, sanctions, reputational damage and, in some cases, imprisonment.
Recently, KYC has expanded beyond the financial industry. Non-profit organisations, virtual asset dealers and companies in other industries have begun to comply with KYC guidelines. As KYC plays a significant role in the business world, understanding its importance is vital to protecting your business, satisfying your customers and preventing crime.

Benefits of KYC
- Understanding your clients: By verifying customers, companies have a better understanding of their clients’ financial profiles.
- Risk assessment: This helps companies assess the risk involved before entering into a business deal.
- Long-term relationship: Companies can make informed decisions regarding the suitability of clients and what it might take to maintain a business relationship with them.
- Builds mutual trust: KYC ensures a greater level of trust and transparency between both parties.
- Regulatory compliance: KYC processes are modular, so they can easily be expanded with add-ons or security checks to fit the required guidelines. It is a small investment that ensures your company and its clients remain safe.
On a broad scale, KYC is also beneficial for customers. These regulations are in place to prevent criminal acts, such as terrorist financing; thereby ensuring that wider markets and economies remain safe.

KYC Process
The KYC process is generally comprised of 6 steps:
- 1. Data collection
- 2. Document checks
- 3. Information validation
- 4. Risk assessment
- 5. Client approval
- 6. Ongoing monitoring and record maintenance
There are several different KYC programs that can be implemented. Choosing the right one is a critical decision. Unsuitable KYC programs can lead to non-compliance penalties. The appropriate selection is dependent upon the type of organization.
KYC PROCESS Main components of KYC
Customer Identification Program (CIP)
The Customer Identification Programme is the most important component of the KYC framework: the verification of a customer's identity. In order to prevent spoofing and ensure that the customer is who they say they are, each individual or legal entity must be verified. In the case of the latter, the beneficial owners must be verified.
Customer identification includes, but is not limited to, data collection, document checks, identification and verification, sanctions list checks, etc. Documents, especially ID cards, are usually verified using a document reader and document verification software.
Customer Due Diligence (CDD)
CDD collects additional client information to assess the individual's risk factor. This information enables you to make an informed decision about a potential client. It also ensures that the information is reliable and comes from a valid source.
Higher-risk clients typically require more rigorous identification checks, which can take significantly longer.
Enhanced Due Diligence (EDD) / Continuous Monitoring
Once a customer has passed the initial screening, their activity and status will continue to be monitored. This may include: transactions, sanctions lists and media coverage. The scope and frequency of EDD will depend on the risk profile of the customer.
In order to maintain a KYC-compliant relationship, EDD keeps customer profiles under constant review.
Record Maintenance
Keeping records of the initial KYC process and ongoing transactions is an important step.
This will ensure that you will be able to identify any illegal activity that may occur in the future. If you come across any illegal transactions, terrorist funding, etc., it must be reported immediately to the relevant authorities.
It is recommended that you keep customer records for at least 5 years.
Reporting
If suspicious activity occurs, it should be reported immediately. Having a set of procedures in place will enable you to deal with the situation quickly with the appropriate authority.

Digitalisation of KYC
Prior to the introduction of eKYC, verifying a customer's identity required a face-to-face meeting to manually check the customer's identification documents, or a third-party verification of key legal documents. Alternatively, knowledge-based authentication (KBA) was used. Unfortunately, all of these processes are less efficient, more costly and leave more room for human error.
To improve the accuracy of KYC, the verification process has been digitised. Modern eKYC conventions include, but are not limited to
- Security checks (biometrics)
- Other technologies (AI or NFC)
Digital KYC procedures streamline the customer onboarding process. In a matter of minutes, the customer can complete the verification process from anywhere.
In addition to quickly verifying POI and POA documents, the demographic data of the document holder can also be integrated into a Customer Relationship Management (CRM) system. This makes customer data easily accessible for ongoing monitoring and record keeping.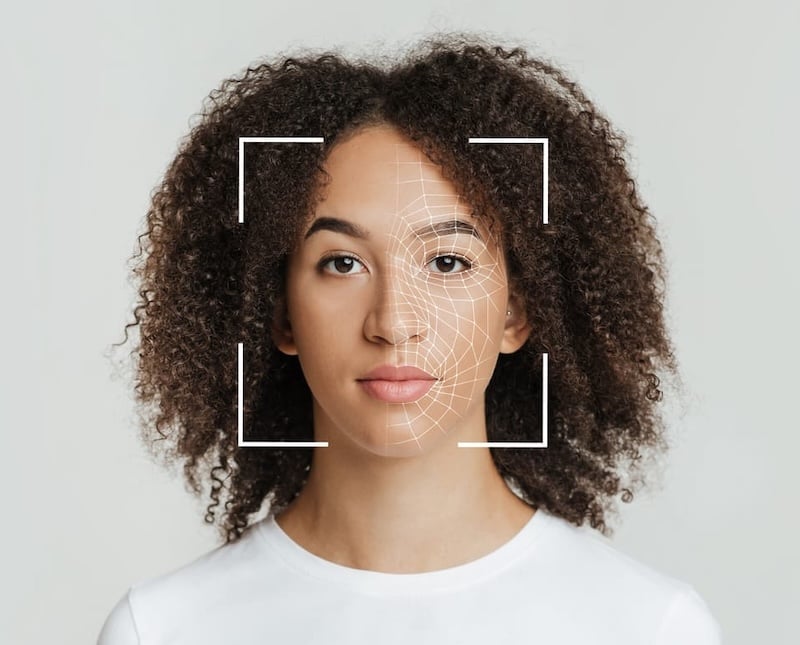
KYC Requirements
KYC has a general set of requirements along with country specific regulations. Moreover, these basic requirements differ from industry to industry – the financial industry being the strictest among them.
- Facial verification – facial verification ensures the live presence of the individual (to quickly and effectively identify spoof attacks).
- Document verification – document verification ensures that the government-issued ID is neither forged, invalid, nor faulty. It is common for institutions to request more than one form of ID (i.e. birth certificate, social security card, passport, driver’s license, etc.) to confirm the customer’s identity.
- Address verification - address verification validates the address on government-issued identification documents against Proof of Address (POA).
KYC Documents
To complete the three above-mentioned stages of verification, several different documents are required. Upon successful verification of the customer’s identity, both parties may proceed to the next stage of the onboarding process.
For the first stage, facial verification, a document containing a picture of the customer, such as an ID card, must be provided. For the second stage, the customer must provide Proof of Identity (POI) The second document required for Proof of Identity (POI), which may be any other government-issued document with a picture on it, such as a driver’s license. Both documents are compared against each other to confirm that neither POI document was falsified. The third, and final stage of the KYC process, requires the customer to provide a document for Proof of Address (POA).
Note: the above-mentioned requirements do not suffice for all KYC processes. This outline is solely intended to provide a basic understanding of the common guidelines set forth for the execution of KYC processes.
- Passport
- Identification Card (government-issued ID)
- Driver's License
- Residence permit
- Employee ID card
- Student ID card
- Health insurance card (with photograph)
- Residence permit or government-issued ID card
- Passport
- Driver's License
- Utility bill that is not more than 6 months old (e.g. a bill such as, water, electricity, gas, telephone, wireless, etc.)
- Bank Account Statement
- Credit Card Statement
- House Purchase deed
- Lease agreement (along with last 3 months rent receipt)
- Employer’s certificate for residence proof
- Income Tax Returns
- Salary Slips
- Bank Statement
GUIDELINES KYC Regulations
In recent years, the European Commission has established a set of KYC guidelines that form the basis for KYC in all EU member states. However, as Europe is too large for one organisation to ensure compliance for all firms, each country still maintains its own regulatory authority and variations of legislation.
In Europe, the regulatory framework for the financial sectors is governed by 5AMLD (5th Money Laundering Directive) and eIDAS (electronic identification, authentication and trust services).
5AMLD ensures that all EU member states have the same understanding of money laundering. As the KYC requirements are virtually the same, companies can more easily extend the reach of their products and/or services to a wider range of potential customers.
5AMLD has also established a reference framework for eKYC processes to assist businesses in onboarding remote customers.

Examples in Europe:
- Germany: The Federal Financial Supervisory Authority (BaFin)
- Switzerland: Financial Market Supervisory Authority (FINMA)
- Italy: Banca d’Italia
- United Kingdom: The Money Laundering Regulations
Examples in other countries:
- US: Financial Crimes Enforcement Network (FinCEN)
- Canada: The Financial Transactions and Reports Analysis Centre of Canada (FINTRAC)
- Australia: Australian Transaction Reports and Analysis Centre (AUSTRAC)
- India: Reserve Bank of India
- South Africa: The Financial Intelligence Center Act 38 (FICA)
The PXL Vision Solution
Understanding the fundamentals of KYC is the first step to making an informed decision about which identity verification solution is best for your organisation. To avoid the risk of non-compliance penalties, ineffective KYC processes and customer churn, PXL Vision has developed a fast and easy-to-use identity verification solution using state-of-the-art machine learning intelligence and AI technology. Our solution is designed to be configured to meet the specific needs of each organisation.
The PXL Vision solution
The PXL Vision solution
- Utilizes high-efficiency, precise AI technology
- Verifies customer in 30 seconds or less
- Accurately performs POI and POA checks

PXL Vision Document Checks
PXL Vision Document Checks
After full integration and custom configuration of the PXL Vision solution, customers can easily complete their eKYC checks. The general steps include
- Scan the required document(s) with a smartphone camera
- Taking a short selfie video
- Submit and complete

PXL Vision process
PXL Vision process
- Check MRZ: We pull information from the machine-readable code lines (MRZ) and run several checks on them.
- Examine the visual inspection zone (VIZ): We review the remainder of the document or VIZ.
- Assess authenticity: We run several security checks and analyze hundreds of visual key features to ensure that the document is real.
- Read biometric NFC chip, if available: This allows us to read information from the document. We also make sure to inspect the chip to confirm that it has not been tampered with.
PXL Vision offers two core identity verification solutions: PXL Ident® and PXL Pro. Our primary solution, PXL Ident®, is a user-friendly SaaS solution that can be individually adapted to local KYC regulations.

POA check
POA check
To perform a POA check, we use an API from a third party service provider. This implementation makes it possible to follow through with a POA check anywhere in the world while maintaining accordance with the KYC guidelines of your country.
.png?width=800&height=533&name=Phone_Hands_Typing%20(1).png)

Summarizing the KYC principle:
- The KYC process is an approach that is particularly suitable for banks and financial institutions
- Profiles of potential customers are examined to ensure that they do not engage in illegal activities with their open business accounts.
READ MORE More on the topic of KYC

KYC Check
Find out how PXL Vision can make the KYC check a easy for you. A secure KYC check optimises your processes and helps companies to prevent money laundering and corruption.
.png?width=800&height=533&name=Phone_Hands_Typing%20(1).png)
KYC Document
Find out what a KYC document is and how PXL Vision can verify it for you quickly, easily and securely. Discover the benefits.
Secure and seamless KYC with PXL Vision
KYC compliance is an integral part of the financial industry, but its importance is expanding into other areas of the business world. The main purpose of KYC is to protect companies, institutions and customers by preventing potential crimes.
PXL Vision's identity verification solutions can simplify the KYC process and eliminate human error. Our solution is designed to reduce risk and costs, while improving compatibility with your business processes and convenience for your customers.
.png?width=126&height=101&name=logo%20(2).png)
.png?width=63&height=51&name=logo%20(6).png)




